Securing Your
Digital Infrastructure
Enterprise-grade cybersecurity consulting, penetration testing, and compliance services for organizations that cannot afford to be breached.
Consultant-Led
Humans run every test. No scanner-only reports.
Audit-Grade Output
Reports QSAs and regulators accept without rework.
NDA-First
Encrypted artifacts, need-to-know access throughout.
Outcome-Aligned
We measure success by reduced risk, not page count.
Elite Security Experts You Can Trust
CyberAlpha is a premier cybersecurity consultancy staffed by certified security professionals who have defended organizations across critical industries worldwide — from FinTech to Healthcare, from SaaS to Government.
We specialize in breaking things safely: our adversarial mindset means we find your vulnerabilities before real attackers do. Beyond testing, we partner with your teams to build lasting security postures that scale with your growth.
Every engagement is shaped around your unique risk landscape — because in cybersecurity, one size never fits all.
Our MethodologyOur Cybersecurity Services
From penetration testing to compliance certification — we cover every layer of your security posture.
Security Testing
Infrastructure, web, mobile, and API penetration testing — OWASP Top 10, business logic, and real attack-path assessments.
Learn MoreSource Code Review
Manual security-focused code review integrated with SAST tooling for secure SDLC.
Learn MorePCI-DSS Compliance
End-to-end PCI-DSS gap assessment, CDE mapping, and QSA-ready documentation.
Learn MoreRed Team Operations
Full-scope adversary simulation using MITRE ATT&CK TTPs.
Learn MorePhishing Simulation
Multi-vector phishing campaigns with employee awareness benchmarking.
Learn MorePatching as a Service
Managed vulnerability remediation across OS, network, containers, and third-party stacks with audit-ready evidence.
Learn MoreRigorous Testing, Real Results
We simulate real-world attacks across your entire attack surface — so you know exactly where you stand.

Internal & External Infrastructure Testing
Our certified testers systematically attack your network perimeter and internal infrastructure just as an APT group would — uncovering misconfigurations, open ports, vulnerable services, and lateral movement paths before attackers can exploit them.
Request AssessmentRed Team Operations
Full-scope adversary simulation targeting your people, processes, and technology. Our red team employs sophisticated TTPs from the MITRE ATT&CK framework to test your detection and incident response capabilities under realistic attack conditions.
Learn About Red Teaming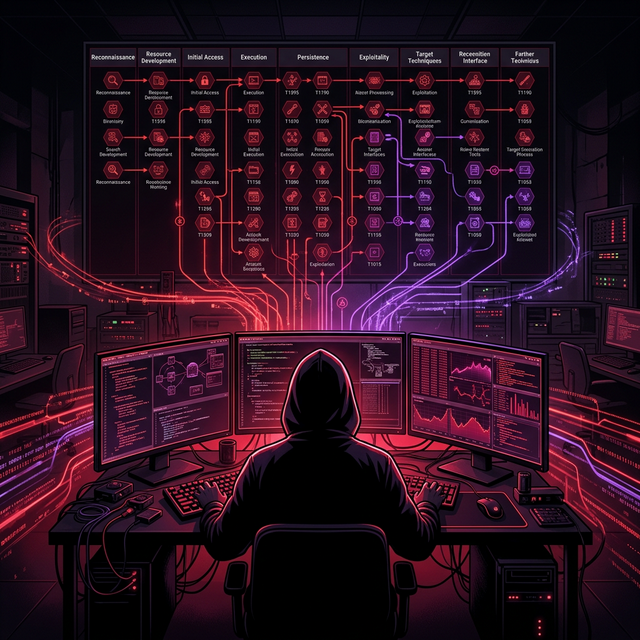
Compliance & Certifications
Navigate complex regulatory landscapes with confidence. We manage your compliance programs end-to-end.
PCI-DSS
Secure payment card processing
ISO Certifications
27001 / 27701 / 42001 / 22301 / 9001 / 14001 / 45001 + more
SOC Certifications
SOC 1 / 2 / 3 — Type I & II
GDPR
Data protection & privacy
HIPAA
Healthcare data security
CISA Audit
Information systems auditing
IS Audit
IT infrastructure review
Surveillance Audit
Continuous compliance monitoring
Cyber Risk is Accelerating
Adversaries innovate daily. Defenders that wait become headlines.
From First Call to Final Report
A smooth, transparent flow combining our engagement phases and security methodology — every step from discovery scoping through remediation validation.
Initial Consultation
Confidential call to understand your security goals, environment, and risk appetite.
Scope Definition
Collaborative definition of engagement scope, timeline, and rules of engagement.
Discovery
Asset enumeration and attack surface mapping.
Threat Modeling
Risk profiling and threat actor analysis tailored to your environment.
Testing
Active exploitation and vulnerability verification by certified experts.
Reporting
Executive + technical reports with CVSS scoring and proof-of-concepts.
Debrief
Live debrief session walking through findings with your team.
Remediation
Fix guidance and re-test validation support until issues are closed.
Why Organizations Choose Us
We combine technical excellence with deep business acumen to deliver security outcomes that matter.
Certified Experts
OSCP, CISSP, CEH, and CISA certified security professionals.
Comprehensive Coverage
End-to-end security across infrastructure, applications, and compliance.
Industry Experience
12+ industries served including FinTech, Healthcare, and Web3.
Fast Turnaround
Rapid engagement initiation with SLA-bound delivery timelines.
Detailed Reports
Executive summaries and developer-ready remediation guidance.
Ongoing Support
Post-engagement support for queries, re-testing, and advisory.
Security Expertise Across Every Sector
From regulated finance to bleeding-edge Web3 — our security specialists understand the unique threat landscapes and compliance requirements of your industry.
FinTech & Banking
PCI-DSS, SOC 2, and penetration testing tailored for payment processors, neo-banks, and financial platforms.
Healthcare & MedTech
HIPAA compliance, medical device security, and EHR system penetration testing for healthcare organizations.
SaaS & Cloud
Cloud architecture reviews, API security, and DevSecOps integration for cloud-native SaaS platforms.
Government & Public Sector
Security audits, IS audits, CISA assessments and compliance frameworks for government organizations.
E-Commerce & Retail
PCI-DSS compliance, web app security, and fraud risk assessments protecting consumer data at scale.
Manufacturing & Industrial
SCADA/ICS security, OT network assessments, and IoT device testing for industrial environments.
Web3 & DeFi
Smart contract audits, DeFi protocol security reviews, and blockchain infrastructure hardening.
EdTech & Education
Securing student data, LMS platforms, and digital learning environments against breaches.
Telecom & Media
Network security assessments, data privacy compliance, and API security for telecom infrastructure.
Insurance & Legal
Data protection audits, secure document management, and compliance for regulated legal and insurance firms.
Energy & Utilities
Critical infrastructure protection, SCADA security, and OT/IT convergence testing for energy operators.
Real Estate & PropTech
Smart building security, tenant data protection, and cloud platform security for modern property tech.
Don't see your industry?
We work with organizations across all sectors. Talk to us about your environment.
Meet Our Security Experts
Certified professionals holding industry-leading credentials across penetration testing, red teaming, and compliance.

Latest Security Insights
Research, guides, and threat intelligence from our security experts.
 Penetration Testing
Penetration TestingTop 10 OWASP Vulnerabilities in 2025 — What CISOs Must Know
A deep dive into the latest OWASP Top 10 list and how modern applications remain vulnerable to classic attack patterns.
 Compliance
CompliancePCI-DSS v4.0 Transition Guide for FinTech Organizations
Everything you need to know about transitioning to PCI-DSS version 4.0 before the March 2025 deadline.
 Web3 Security
Web3 SecuritySmart Contract Auditing: Lessons from $2B in DeFi Exploits
An analysis of the most significant DeFi security failures and lessons for blockchain developers.
Ready to Secure
Your Business?
Join 500+ organizations that trust CyberAlpha to protect their most critical digital assets.
- Confidential 30-min discovery call
- Custom scope & SoW within 48h
- NDA-first onboarding
Start Your Security Journey
Whether you need a penetration test, compliance audit, or ongoing security advisory — we're here to help. Reach out and we'll respond within 24 business hours.